.webp)

First-ever worm that attacked the internet : Morris Worm
Colombo (News 1st): Our connected world comes with countless risks. Viruses, worms, spyware, ransomware, backdoors, trojans: The language of cybersecurity is relatively new, but we have quickly become fluent. The misuse of technology has become the darkest danger of the digital age. Bad actors, emboldened by our inability to properly secure crucial systems and networks, are launching increasingly sophisticated attacks. No system is safe.
But in the beginning, the very, very beginning computers inspired utopian visions of a better future, a world in which we were all digitally connected to one another and living in harmony.
Then came the Morris Worm.
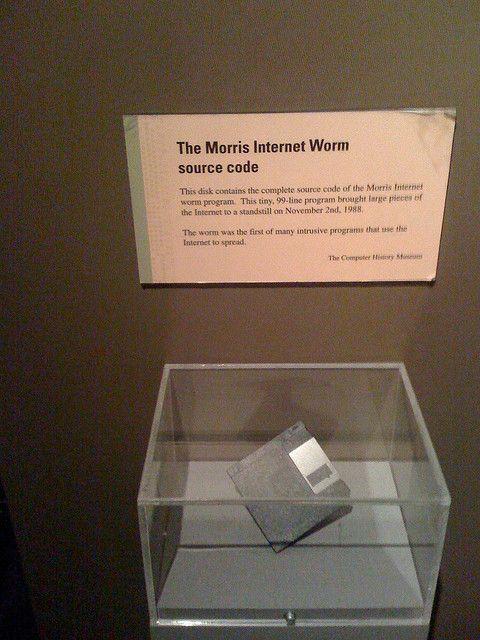 Floppy Diskette containing the source code for the Morris Worm held at the Computer History Museum.[/caption]
Floppy Diskette containing the source code for the Morris Worm held at the Computer History Museum.[/caption]
What is a worm, is it a kind of a virus?
Well, it is sort of, but not exactly the same, a worm is a malicious, self-replicating program that can spread throughout a network without human assistance. They cause damage similar to viruses, exploiting holes in security software and potentially stealing sensitive information, corrupting files and installing a back door for remote access to the system, among other issues. But remember worms are not viruses. Viruses need a host computer or operating system, however, the worm program operates alone.So then what was the first-ever worm that attacked the internet?
On November 2, 1988, at around 8.30 pm, a maliciously clever program was unleashed on the Internet from a computer at the Massachusetts Institute of Technology (MIT). This cyber worm, which was later known as “Morris Worm” was soon propagating at remarkable speed and grinding computers to a halt. Within 24 hours, an estimated 6,000 of the approximately 60,000 computers that were then connected to the Internet had been hit. As mentioned earlier computer worms, unlike viruses, do not need a software host but can exist and propagate on their own. The rogue program had infected systems at a number of the prestigious colleges and public and private research centres that made up the early national electronic network. This was a year before the invention of the World Wide Web. Among the many casualties were Harvard, Princeton, Stanford, Johns Hopkins, NASA, and the Lawrence Livermore National Laboratory. The worm only targeted computers running a specific version of the Unix operating system, but it spread widely because it featured multiple vectors of attack. For example, it exploited a backdoor in the Internet’s electronic mail system and a bug in the “finger” program that identified network users. It was also designed to stay hidden. The worm did not damage or destroy files, but it still packed a punch. Vital military and university functions slowed to a crawl. Emails were delayed for days. The network community laboured to figure out how the worm worked and how to remove it. Some institutions wiped their systems; others disconnected their computers from the network for as long as a week. The exact damages were difficult to quantify, but estimates started at $100,000 and soared into the millions. As computer experts worked feverishly on a fix, the question of who was responsible became more urgent. Shortly after the attack, a dismayed programmer contacted two friends, admitting he’d launched the worm and despairing that it had spiralled dangerously out of control. He asked one friend to relay an anonymous message across the Internet on his behalf, with a brief apology and guidance for removing the program. Ironically, few received the message in time because the network had been so damaged by the worm. Independently, the other friend made an anonymous call to The New York Times, which would soon splash news of the attack across its front pages. The friend told a reporter that he knew who built the program, saying it was meant as a harmless experiment and that its spread was the result of a programming error. In follow-up conversations with the reporter, the friend inadvertently referred to the worm’s author by his initials, RTM. Using that information, The Times soon confirmed and publicly reported that the culprit was a 23-year-old Cornell University graduate student named Robert Tappan Morris. Morris was a talented computer scientist who had graduated from Harvard in June 1988. He had grown up immersed in computers thanks to his father, who was an early innovator at Bell Labs. At Harvard, Morris was known for his technological prowess, especially in Unix; he was also known as a prankster. After being accepted into Cornell that August, he began developing a program that could spread slowly and secretly across the Internet. To cover his tracks, he released it by hacking into an MIT computer from his Cornell terminal in Ithaca, New York. After the incident became public, the FBI launched an investigation. Agents quickly confirmed that Morris was behind the attack and began interviewing him and his associates and decrypting his computer files, which yielded plenty of incriminating evidence.But had Morris broken federal law?
Turns out, he had. In 1986, Congress had passed the Computer Fraud and Abuse Act, outlawing unauthorized access to protected computers. Prosecutors indicted Morris in 1989. The following year, a jury found him guilty, making him the first person convicted under the 1986 law. Morris, however, was spared jail time, instead of receiving a fine, probation, and an order to complete 400 hours of community service. The episode had a huge impact on a nation just coming to grips with how important and vulnerable computers had become. The idea of cybersecurity became something computer users began to take more seriously. Just days after the attack, for example, USA’s first computer emergency response team was created in Pittsburgh at the direction of the Department of Defense. Developers also began creating much-needed computer intrusion detection software. At the same time, the Morris Worm inspired a new generation of hackers and a wave of Internet-driven assaults that continue to plague our digital systems to this day. Whether accidental or not, the first Internet attack 30 years ago was a wake-up call for the country and the cyber age to come. [caption id="attachment_407552" align="aligncenter" width="480"]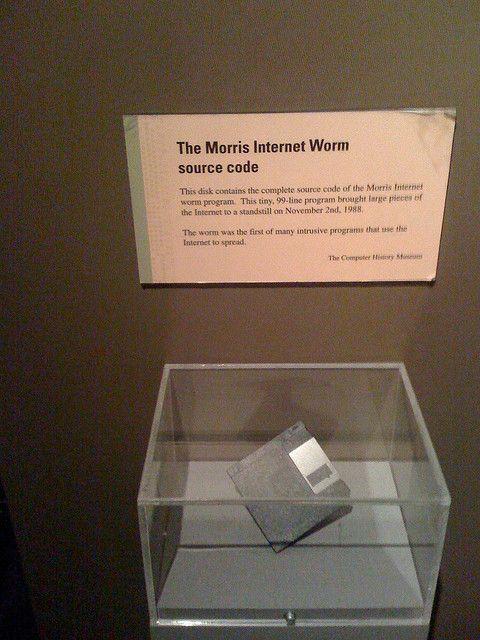 Floppy Diskette containing the source code for the Morris Worm held at the Computer History Museum.[/caption]
Floppy Diskette containing the source code for the Morris Worm held at the Computer History Museum.[/caption]Other Articles
Featured News





.png )


-835300_550x300.jpg)























.gif)